Episode 3 – “Networld War”
3/16/2020 | 55m 37sVideo has Closed Captions
Host Niall Ferguson focuses on the geopolitics of our interconnected world.
Looking at the fight against terrorist networks in Iraq, Russian attempts to divide Americans through social media and the rise of an Internet-powered surveillance state in China, Ferguson shows how our democracies are under threat from outside forces that seek to weaponize the social networks that we invented. He warns of a coming “networld war” that the West may not win.
Problems playing video? | Closed Captioning Feedback
Problems playing video? | Closed Captioning Feedback
Episode 3 – “Networld War”
3/16/2020 | 55m 37sVideo has Closed Captions
Looking at the fight against terrorist networks in Iraq, Russian attempts to divide Americans through social media and the rise of an Internet-powered surveillance state in China, Ferguson shows how our democracies are under threat from outside forces that seek to weaponize the social networks that we invented. He warns of a coming “networld war” that the West may not win.
Problems playing video? | Closed Captioning Feedback
How to Watch Niall Ferguson’s Networld
Niall Ferguson’s Networld is available to stream on pbs.org and the free PBS App, available on iPhone, Apple TV, Android TV, Android smartphones, Amazon Fire TV, Amazon Fire Tablet, Roku, Samsung Smart TV, and Vizio.
Buy Now
♪♪ -Connectivity is a human right.
-Many of the details being spread online are simply not true.
-False claims -- there was no knife, like many online blogs are saying.
-They're fake news.
[ Gunshots ] -You may have been startled or confused by what you've seen online recently -- fake news, extreme views... -This has got to stop.
They are not compatible with our culture.
They hate us.
They don't want to be Americans.
-...polarization, information wars, an epidemic of trolling and so-called hate speech.
♪♪ All of this has been made possible by one thing -- the exponential growth and exploitation of online social networks... ♪♪ the networks that all of us are increasingly entangled in and use, and sometimes abuse, in our daily lives.
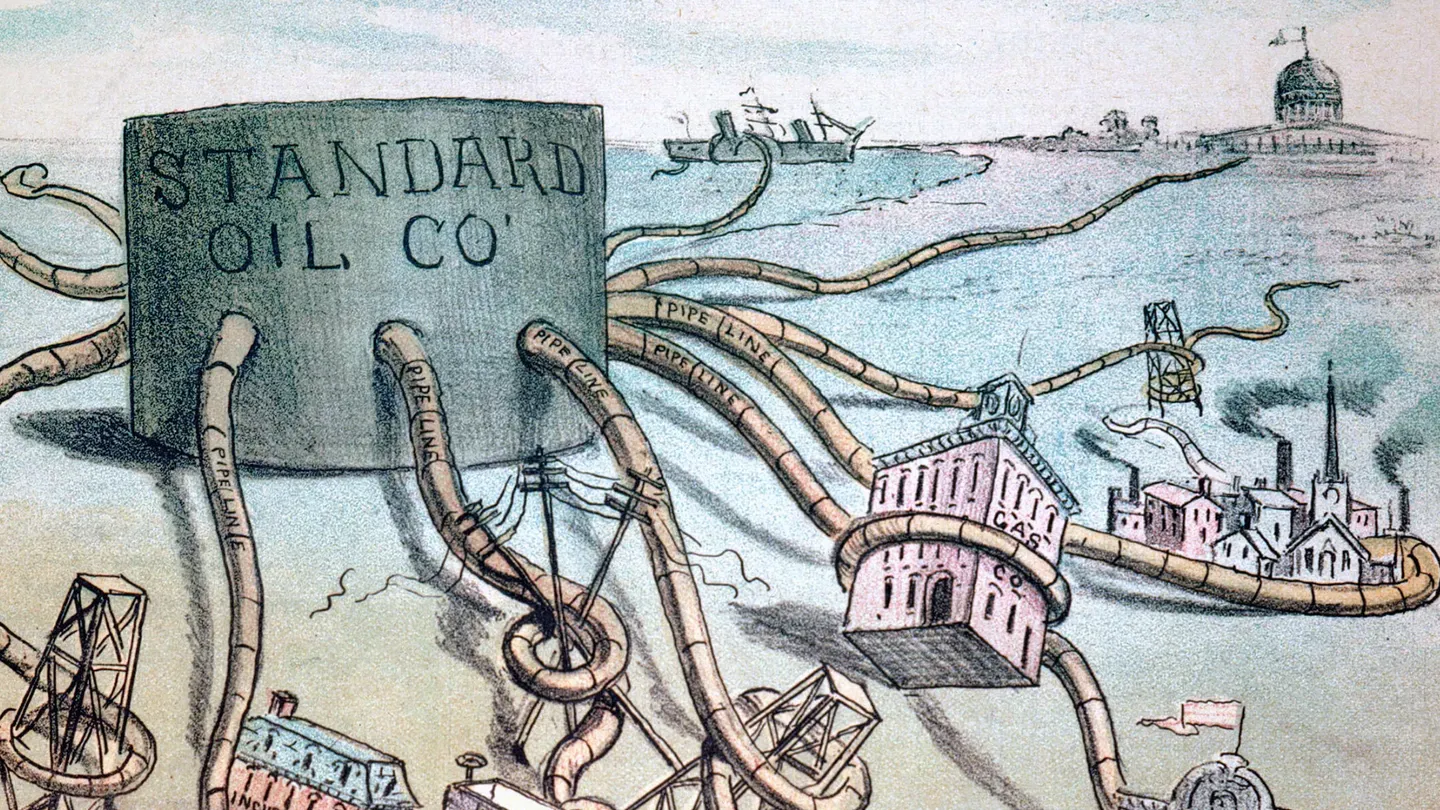
♪♪ As we saw in the first two episodes of this series, this networld might not be the connected utopia we were promised, but is, instead, an increasingly polarized and unstable place where truth is at a disadvantage and giant monopolistic network platforms control the personal data that we produce.
♪♪ We've looked at the political perils of networld.
Now, however, we need to ask a bigger question: [ Gunshots ] Are our networks coming under attack?
Are we heading for a networld war?
♪♪ [ Beeping ] [ Electricity buzzing ] -For a time, it seemed as if the network world would also be a more democratic world.
The masters of Silicon Valley assured us that their technology would render dictatorship obsolete and create a new and transparent global community where all netizens would be free to speak their minds and exchange their views.
Well, it hasn't quite worked out that way.
[ Rapid gunfire ] Now, as we'll see in this film, we find our networks under attack by foreign forces intent on riling and dividing us... [ Gunshot ] ...which raises three rather important questions.
[ Explosion ] Why are the networks we built so open to attack?
-Faceless accounts, time and again.
Faceless accounts, time and again.
-And will the next world war be a cold war against rival Chinese networks?
-You have all of the cultural issues, the business issues, the military issues, the censorship issues playing, so we shouldn't be surprised that this fight is happening now.
-Battalion!
[ Marching ] -But the third question is: Why does it take a network to defeat a network?
[ Boots stomping ] -Left shoulder!
-March!
[ Call and response ] -Conflicts in the past tended to be between hierarchically organized states and their armies.
Orders were handed down by kings or generals and transmitted through the ranks to the front line.
♪♪ [ Gunshot ] But already -- and it will be increasingly true in the future -- our enemies include decentralized networks, which are much, much harder to destroy than we had thought.
-US warships and planes -- there were F-117 stealth bombers involved -- launched the opening salvo of Operation Iraqi Freedom.
[ Missile whooshes ] [ Explosion ] -After the 9/11 attacks, the Bush administration's first reaction was to go after the enemies' protectors in Afghanistan... [ Explosion ] ♪♪ [ Rapid gunfire ] and then to launch a large-scale military [ Explosion ] invasion of Iraq in 2003.
[ Explosions ] Because that's the kind of thing a hierarchical structure, like the US government, is preprogrammed to do.
♪♪ The job seemed simple enough when General Stanley McChrystal arrived in Iraq as commander of Special Forces in 2003.
-I would anticipate that the major combat engagements are over because the major Iraqi units on the ground cease to show coherence.
[ Explosions ] -But that was before they worked out who, and what, the new enemy was.
♪♪ -We saw the appearance of a terrorist network, which ultimately became al-Qaeda in Iraq, and we wanted to focus on them and so, we looked at what they had to look like and that was a pyramid-shaped hierarchy that all terrorist organizations in the past have been based on.
And, really, it was probably about January or February 2004 when the light goes on: It ain't there.
[ Explosion ] [ Dog barking ] In the early part of it, we thought, "Well, if we get the number two, the emir of this area, the leader of this area, what they'll do is they'll stumble.
They'll have to rebuild that and we'll do that," and what happened is, instead, they just do this organic adaptation and you don't see them slow down.
You see them keep growing.
In fact, sometimes, they seem to gain momentum.
[ Horn bleats ] -Something had to change.
[ Horn bleats ] To confront this spreading network, McChrystal had to transform his top-down command structure to replicate the enemy's dispersion, flexibility, and speed.
-We figured out that the enemy was really a network and the great strength that they had was they could inform each other extraordinarily quickly, they could adapt to the information, and they could react and cause things to happen extraordinarily fast.
And we decided, well, we needed to become a network, too, and so the mantra inside the command became, "It takes a network to defeat a network," and we are gonna have to be a better network than they are.
Now, the challenge came: How do you get all of the information and wisdom that happens here, not just to the top, but down in everybody?
How do you get the information, the contextual information, to flow down and to flow across, so that the people actually doing the work, making the decisions close to it, have the big picture and the local picture, so they could act within contextual understanding that makes them effective?
And you go, "Wow.
How could you possibly do that?"
And the answer is information technology.
The same thing that made all this harder also offers us some fixes to how to do it.
You now have the ability to share information in a way that we never did before and so, suddenly, the ability to network across that organization to respond to those threats, to deal with them so much faster, becomes the defining characteristic.
[ Rotors whirring, whining ] -Al-Qaeda in Iraq seemed beaten; its network, destroyed.
But after the rapid withdrawal of US forces from Iraq and McChrystal's redeployment to a new command in Afghanistan, the remnants of al-Qaeda's network formed the initial cluster of what became an even larger, and more bloodthirsty, network.
-[Singing in Arabic] -This was Islamic State of Iraq and Syria... ♪♪ ...ISIS.
♪♪ [ Chiming ] For years, the American military developed a doctrine of cyber warfare, which emphasized the role of viruses and malware to spy on, and potentially control, an enemy's computer network.
The fear was that a hostile pah would hack into the software running on America's critical infrastructure.
But all this emphasis on cyber warfare led the West to neglect an alternative form of network warfare: information war.
♪♪ First, al-Qaeda; and then, ISIS; attracted tech-savvy recruits who knew how to use new technology, in particular, ubiquitous, multilingual, and unregulated social networking platforms, like Facebook and Twitter, to disseminate their own, toxic brand of Islam.
♪♪ Khuram Zaman, who runs a digital marketing company in Washington, D.C., knows this from firsthand experience.
He had a childhood friend who was seduced by al-Qaeda's fundamentalist message.
♪♪ -So that's Samir Khan.
His full name is Samir Zafar Khan.
We became really close friends.
Both of our parents were very involved with certain Muslim organizations that we kind of would attend their conferences annually.
We both read the same literature, but how we viewed the world was a little bit different.
When I went to law school, I sort of lost touch with Samir and, when I came back, I found out he had actually left the United States and he had gone to Yemen to join Anwar Awlaki, who had established al-Qaeda in the Arabian Peninsula.
[ Gunshot ] Samir started creating magazines for them.
Over here, you can see that it's called Inspire and talks about how you can derail a train to commit a terror attack.
♪♪ -Level, actually, and here comes power.
-This made Samir a target.
-At one two.
Clear to land.
-It was a pivotal moment because the jihadist literature at that time was very old-fashioned and what he did was he made it relevant to the next generation, people in our age group, people that consumed social media.
-Payload sits positioned [indistinct] for landing, a video source to the right.
Okay.
-And then, on September 30, 2011, this happened.
[ Explosion ] -One day, while he was in Yemen, there was a drone attack that was targeting Anwar Awlaki, and Samir was killed in that attack, along with Anwar Awlaki.
[ Explosion ] -Awlaki was killed along with three others, including another American, Samir Khan.
Khan, from North Carolina, was the chief propagandist for Awlaki's terror group.
♪♪ -Using his computing skills, Zaman decided to look in-depth at Islamic State social media propaganda.
He set up a program to track all ISIS Twitter accounts and used this metadata to construct a network of their operations.
♪♪ The results were extraordinarily revealing.
-They're very, very social media savvy.
They're very technologically savvy.
You could see here that ISIS, on Twitter, they had about 700,000 accounts at their peak.
What I saw was a lot of the jihadists online, many of them boast about being a jihadist.
They don't shy away from it.
So, they would have a picture of a gun and a black flag or a line, or the name Shahid, which means "martyr," and so it's very obvious that they're pro-ISIS.
[ Blast ] -As we saw with al-Qaeda in Iraq, [ High-pitched whine ] attacking the most obvious targets doesn't always destroy the network.
[ Blast ] When it came to ISIS propaganda, the US military had got the wrong people.
-What this network analysis showed was those were not the network nodes.
The people that were the center of the networks were people called WarReporter.
WarReporter is an individual who claims to be a journalist and he would go out and say, "I'm just reporting the news," but the news happens to be all pro-ISIS.
-What Khuram Zaman was getting was also a lesson in network structure.
The big tech companies had applied the business mantra of "Move fast and break things" to increase the number of users, get them hooked, and then ramp up advertising revenue.
But this meant prioritizing easy access with a low security threshold.
The developers had left the platforms wide open to exploitation by bad actors.
ISIS was far from the only bad actor to see this opportunity.
By the time the presidential campaign of 2016 came along, a new breed of hackers had seen the potential of social media.
Their goal was not to recruit the next generation of extremists, but to infiltrate Western politics itself.
And they aim to do this by ruthlessly exploiting the vulnerability of social networks.
♪♪ ♪♪ It was the bad luck of the usually peaceful town of Twin Falls, Idaho, to be one of the targets, the eye of a perfect storm of orchestrated fake news.
♪♪ Like many towns in America, Twin Falls had recently taken a number of Iraqi and Sudanese refugees under a federal resettlement program.
Nathan Brown was a reporter for the local paper at the time, covering small-town politics and Rotary Club meetings.
-We're in the Fawnbrook Apartments.
This is where, in June 2016, three refugee boys assaulted a five-year-old girl in one of the laundry rooms here and, when news of that came out, it kind of triggered a bit of a political firestorm, I guess you'd say.
-Tonight, widespread rumors circulating in the Twin Falls area that three Syrian refugees raped a young child.
-The girl was American and, like most people in Twin Falls, white.
The boys were refugees and it was that fact that led to a feeding frenzy of fake news in the town.
-The presidential election was going on and immigration and refugee resettlement were major issues in that election, so it was as on people's minds here a little bit more, maybe, than it was in some other parts of the country.
♪♪ -Shawn Barigar is mayor of Twin Falls.
He was 2,000 miles away when the news broke.
♪♪ -Our police department was investigating it.
It was going through the regular process and, somewhere along the way, someone remanufactured that story to be, "Young five-year-old girl raped at knifepoint by refugees."
I was in Washington, D.C., at a conference.
♪♪ -It turned out that online accounts of the alleged crime were fundamentally inaccurate.
None of the boys were Syrian, the girl was not raped, and there was no knife involved.
-The story has spread like wildfire on social media and several blogs.
-"6 on Your Side" has confirmed an incident did take place, but, investigators say, many of the details being spread online are simply not true.
-In fact, the prosecutor's report stated that one boy touched the girl and another recorded it with a cell phone.
The boys were convicted and sentenced to probation and counseling.
-I get a phone call that I'm on the front page of The Drudge Report and, by the time I was home the next day, it was everywhere.
-The Drudge Report, with other news websites, was a key online purveyor of such stories, which were implicitly supportive of Donald Trump's campaign for the US presidency.
-Initially, they contained a lot of, well, horrific details, like, you know, saying that these boys had held this girl at knifepoint, that they'd raped her, that one of the boys' fathers had watched and high-fived them after, things like that.
-And we were up against a machine, like Breitbart and Facebook and Twitter, and whoever is sitting in their basement on their computer, just manufacturing this vision of Twin Falls that isn't reality.
♪♪ -What was happening was that the pro-Trump website Breitbart News and its executive chair, Steve Bannon, had spotted that the Twin Falls story aligned perfectly with their narrative about the consequences of uncontrolled immigration, especially Muslim immigration.
♪♪ Where Bannon led, countless social media trolls and bots followed.
-It felt like the entire universe knew about this and was focused on Twin Falls.
♪♪ -In fact, Shawn Barigar and the town of Twin Falls were under bombardment by a virtual army of self-replicating bots, fake social media accounts designed to disseminate and amplify fake news.
This was information warfare and they were the battlefield.
♪♪ If the intention was to divide the people of Twin Falls, it certainly seemed to be working at a meeting in the city hall a few days after the story broke.
-This has got to stop!
They are not compatible with our culture.
They hate us!
They don't want to be Americans.
-This is my country, damn it, and bringing in these people from other countries, if they don't abide by our rules, they need to get the hell back to their country.
♪♪ -So, the call from my wife was that she had received a death threat, very threatening voicemail on her voicemail at work, um, you know, asking how she would like it if marauding Muslims came and raped her children and killed her at her home.
♪♪ I don't know.
I mean, really thinking through all of it, that's maybe the scariest thing in all of this, is that it's so easy to just throw stuff out there, and I guess the human nature inclination is it tends to be bad.
♪♪ -In fact, it wasn't just politically motivated Americans who were manipulating the news about Twin Falls.
♪♪ What Mayor Barigar didn't know was that another, hidden force was spreading false rumors, unchecked, on social networks, like Facebook.
♪♪ On August 27, 2016, at the Twin Falls City Council Chambers, the Secured Borders Facebook group organized the Citizens before refugees protest rally.
♪♪ It looked like American populism in action.
♪♪ But Secure Borders was, in fact, an account set up here, in St. Petersburg, in Russia.
[ Bell tolling ] In a surreal twist which is only possible in today's hyperconnected world, the discontent in Twin Falls was also partly orchestrated from this building, at 55 Savushkina Street, a Russian troll factory housing the Internet Research Agency.
♪♪ Renée DiResta studies how Russian disinformation tactics have penetrated American network platforms.
-They had teams and they had account operators, who they called specialists, and these specialists were trained to run pages and accounts that mimic certain facets of American society, so, in the operations targeting America, they would be instructed in how to communicate effectively as Americans.
-Ben Nimmo is a counterintelligence expert at the Atlantic Council, a Washington-based think tank.
♪♪ -At its peak, the Internet Research Agency was employing 900 people.
We know that it was a four-story building in St. Petersburg that they were operating from.
This was a large-scale operation.
It's looking like this is an operation with access to trained linguists in nine different languages who are nonetheless not translators.
That's a very, very specific threat signature and that's an awful lot of work.
♪♪ -As Facebook's head of security, Alex Stamos was responsible for investigating Russian attacks on his network.
-Building a troll farm is not that easy, right?
The Internet Research Agency had to build this organization full of, you know, disaffected Russian millennials with enough English skills to study American society, to pretend to be Americans.
They had a graphics department.
You know, it is not trivial to build this kinda capability to influence a foreign society.
-Russian meddling in other countries' politics on this scale shouldn't really come as a surprise, especially with a Russian president who's a former KGB agent, for this was a propaganda tactic born in the Cold War.
♪♪ These Cold War propaganda posters were designed for domestic consumption, each side telling its people how terrible life was on the other side of the Iron Curtain.
♪♪ ♪♪ But taking propaganda to the enemy was different.
American psychological operations, PSYOPs, were countered by Soviet active measures, aktivnye meropriyatiya.
[ Eerie music plays ] The Soviets understood that active measures worked best when they had a ring of truth and tallied with Western preconceptions.
♪♪ This was the site of one of their greatest propaganda coups, Fort Detrick in Maryland... [ Metal clanging ] [ Suspenseful music plays ] ...which, in the 1970s, was a secret biological research facility.
♪♪ [ Steam hissing ] According to the Soviets, it was here that CIA agents had created the HIV virus that, by the 1980s, was beginning to claim lives in the gay communities of American cities.
♪♪ -[chanting] What do we want?
-Money for AIDS!
-When do we want it?
-Yesterday!
-What will it do?
-Wipe out AIDS!
-What do we want?
-Money for AIDS!
[ Whistling and applause ] ♪♪ -The story was launched in an apparently scientific paper published first in India.
♪♪ By late 1987, the story had circulated in the media of 80 countries... ♪♪ appearing in over 200 periodicals, in 25 languages, including the Daily Express in England.
This kind of disinformation warfare couldn't save the moribund Soviet Union, nor could it prevent the steep descent of the Russian economy in the 1990s.
But Russia's leaders, especially those with a KGB background, like President Vladimir Putin, didn't forget the effectiveness of active measures and it began to dawn on them that the American Internet was an exceedingly promising new battle space.
♪♪ In 2016, the modern incarnation of aktivnye meropriyatiya became a sophisticated, multimillion-dollar social media operation using hundreds of thousands of fake accounts with the goal of dividing Americans.
♪♪ -What they were really doing, over time, over about two and a half years, was facilitating tribalism.
So, in this particular example, Back the Badge was an Instagram account.
They also had a Facebook page and what they were doing there was it was a page devoted to police officers and the narratives that they were putting out was this notion that here's a community of people, police officers, who were sacrificing so much, were putting their lives on the line, and they're just being treated terribly by the rest of America.
♪♪ -The real trick of Russian social media tactics is to take a divisive issue and play each side against the other.
-And then, on the other side of the narrative, the other thing that you would see in that #police or #cop would be stories like this.
And in this particular image, you have a woman and the names of victims of officer-involved shootings are written across her hair and it says, on the bottom, "We should know their names" and it's asking, "Got justice?"
-Remember: both sides of this conflict were created, not by Americans, but by Russians.
♪♪ For the Russians, 2016 was just the beginning.
In network terms, what happened in the presidential election was that a super cluster of densely interlinked, closely followed accounts systematically disseminated fake news and extreme views on Facebook, Twitter, and the other network platforms.
Facebook has since admitted that the Russians used 470 false identities and took out around 3,000 ads on Facebook and Instagram.
According to Twitter, the Russians tweeted two million times in the run-up to the election.
And it's important not to exaggerate the role the Russians played.
In all, they probably accounted for less than 1% of all the political content online in the election year.
It would be more accurate to say that the network platforms, rather than the Russians, were the decisive factor.
They enabled Americans to wage information warfare on one another and, in particular, they enabled this man to run a highly targeted campaign.
♪♪ As the head of Breitbart News, Steve Bannon had already been involved in the spreading of the Twin Falls fake news story.
He came to see Donald Trump as the only candidate who wasn't afraid to articulate ordinary Americans' fears about immigration.
♪♪ In August 2016, he quit Breitbart to become the chief executive of the Trump campaign.
Crucially, it was Bannon's appreciation of the power of targeted online advertising, a strategy that had been successfully tested already in the Petri dish of Brexit, that enabled him to propel Trump to the White House.
♪♪ Without the Russians, Trump might not have won.
Or, then again, he might have.
It would still have been close, but without Facebook, he'd have stood no chance.
♪♪ By now, we've learned that, to defeat enemy networks, you have to build your own, and that the giant online social networks built by Silicon Valley are exceptionally vulnerable to attack.
But the Russian attacks of the 2016 election pale into insignificance, compared with what we may face in a looming conflict: a cold war with Chinese characteristics.
♪♪ In the new struggle for network power, Silicon Valley is pitted against the Chinese tech capitals of Hangzhou and Shenzhen.
Welcome to the geopolitics of big tech and to the new networld war.
♪♪ ♪♪ [ Horn honking ] Shenzhen, just across the border from Hong Kong in Southern China, is one of the super hubs of today's network world.
♪♪ What's happening here makes it clear that China has done more than just copy what the big American tech companies were able to do in online retail, search, and social networking.
♪♪ For FAANG -- Facebook, Apple, Amazon, Netflix, Google -- read BAT -- Baidu, Alibaba, Tencent.
In some respects, the Chinese have gone further, outpacing their rivals in the United States.
Just look at the stats.
Already, in 2016, Alibaba was able to process three times as many transactions per second as PayPal, its nearest competitor.
Or, let's consider the world record for processing power, measured in terabytes per minute.
In 2013, number 1 was Yahoo, but after that point, it was the Chinese that won gold: Baidu, Alibaba, and Tencent.
As executive chairman of Google between 2001 and 2015, Eric Schmidt led Google into China and then out again, in protest against Chinese state censorship.
♪♪ Let's talk about the geopolitics of all this.
Not many people anticipated that it would be China that would produce companies almost as big as Google and Facebook and Amazon.
Did that come as a surprise to you?
-Fifteen years ago, smart investors understood that China would modernize at a rate of 5%, 6%, 7% a year, that people would skip the old technology and move to mobile phones and apps and games.
People understood that five times more people, plus that kind of economic growth, would make a domestic market that was big enough to fund the kinds of companies we have today.
And out of that came extraordinary business successes, like Tencent, Alibaba, and so forth, the Big Three, as they're known in China.
♪♪ -How did this happen?
How did the Chinese get ahead, when, only recently, they were so far behind?
♪♪ In any apartment block in any city in China where Go, weiqi, is played, you can find the answer.
♪♪ This 2,500-year-old two-player game of encirclement has the most permutations and moves of any game ever invented... ♪♪ ...far more than in chess.
♪♪ Indeed, the number of possible games of Go exceeds the number of atoms in the observable universe.
♪♪ In imperial China, it was considered one of the essential arts for a cultured gentleman scholar.
♪♪ [ Ticking clock tune joins ] ♪♪ In May 2017, the world number 1 Go player, a Chinese teenager called Ke Jie, took on a computer program called AlphaGo.
The program, based on the form of artificial intelligence known as a deep neural network was built in London by DeepMind, a company now owned by Google.
♪♪ Fearful that their champion might lose, the Chinese government banned live broadcast of the contest.
♪♪ Ke Jie was defeated in all three games.
The reaction was immediate and dramatic.
[ Beeping ] This blow to their national pride was as shocking to the Chinese in 2017 as the unwelcome appearance of the Soviet satellite Sputnik had been to Americans 60 years earlier.
♪♪ It had seemed then as if the United States was in serious danger of losing the Cold War.
♪♪ In response, the American government stepped up its investments in military technology, launching the research project that created ARPANET, the direct ancestor of the Internet.
♪♪ Just two months after the defeat of their Go champion, money poured into Chinese artificial intelligence research from venture capitalists and tech juggernauts, like the world's biggest online retailer: Alibaba.
♪♪ Within a year, China was making up 48% of all AI venture funding globally, surpassing the United States for the first time.
♪♪ There's one reason why they could do this.
China has a huge supply of computer engineers.
These students at the elite Tsinghua University in Beijing are just some of the millions studying science and technology in Chinese universities.
They are the shock troops of China's technological catch-up.
♪♪ David Li is professor of Economics at Tsinghua.
He's an expert on the rapid growth of China's network platforms.
♪♪ -To begin with, you have to understand China has the largest, by far, the largest source of engineers, the largest contingent of engineers.
How many?
Let me give you a number, okay?
Each year, China got 3.6 million graduates in the area of science and technology and engineering, out of 8.2 million college graduates each year.
-[Speaking Chinese] -How many in the US?
By my calculation, maximum: 200,000.
Number two: huge, huge number of consumers.
[ Applause ] Number three: Chinese leadership, overall, has a culture of science technology.
In contrast, many of the leaders in the US and the UK are lawyers.
♪♪ -There's another difference, and it's a crucial one.
In China, the relationship between the government and the network platforms is very different, indeed, from that in the West.
Whereas, in the West, we might recoil in horror at the idea of a state-controlled media, in China, it's a very different story.
It's just a cost of doing business.
♪♪ We were given access to the backroom analytics of one of China's largest social media companies, Sina Weibo, a hugely popular sort of joined-up Twitter, Instagram, and Facebook.
-In China, the total user scale in March 2019 is 465 million and as a total in April, there's 2.9 billion monthly feeds being posted, and below that is engagement of this feed and the total monthly engagement on Weibo in April 2019 is 8.3 billion.
♪♪ -The figures really are astonishing.
♪♪ In the month we visited, 465 million people had been online, exchanging gossip and debate on hot topics.
Today's top discussion?
Body shape.
♪♪ Yet, there's no escaping that Weibo, like all other network platforms in China, is ultimately subordinate to the Chinese Communist Party.
♪♪ In effect, the vast quantities of data that Chinese network platforms accumulate from their users are accessible on demand by the state and the networks have to tread very carefully.
♪♪ -I think the Chinese government is very, very savvy, very, very intelligent, in understanding this.
That is, they understand that the platform, a platform, can be a major factor in swaying people's opinion, so that they have to be super careful.
-It used to be thought that the networked age would be as inimical to the Chinese Communist Party as it was to its Soviet counterpart, but that was fundamentally to misunderstand the nature of Chinese politics and society.
[ Camera shutter clicking continuously ] [ Applause ] These seven men, with their dark suits and dyed black hair, run China as a hierarchy, with ruthless top-down control over ordinary people.
♪♪ They are to the Communist Party what the cardinals are to the Roman Catholic Church or the Joint Chiefs of Staff are to the US military.
♪♪ The first priority of the Standing Committee of the Politburo is to address the Communist Party's greatest fear... ♪♪ ...political protest.
♪♪ The Chinese call it dongdàng, "turmoil."
♪♪ -[Speaking Chinese ] -In the past, Chinese leaders relied on the totalitarian system of control built by this man, Mao Zedong.
[ Blast ] [ Explosion ] After Mao won control of China in 1949, at the end of a brutal civil war with the nationalists, he built a surveillance operation so pervasive that it reached into the tiniest nooks and crannies of people's lives.
♪♪ This was the tried and tested method of political control used by all totalitarian states.
♪♪ But, today, the Communist Party hierarchy [ Musical ringtone ] has another weapon at its disposal.
[ Ring ] Whereas social media platforms in the West mine our data to sell our attention to advertisers, in China, these networks have an additional use.
By monitoring what people say, they can not only censor content, but also identify potential troublemakers.
♪♪ ♪♪ Bill Clinton once joked that, for China to regulate the Internet would be like nailing Jell-O to a wall.
But it hasn't quite turned out that way.
♪♪ [ Horn bleats ] ♪♪ If you have the right app on your phone in the city of Langfang, south of Beijing, you can spot every debt defaulter within 500 meters.
♪♪ The redder the radar, the more defaulters.
♪♪ Click on one of them, and you can see who the defaulter is: their full name, their ID number, what street they live in, and how much they owe.
♪♪ [ Modem warbling ] [ Beeping ] ♪♪ This is a deadbeat map, run on Tencents' WeChat social media network, and it's part of China's social credit system, which is far more comprehensive than Western systems of financial credit rating.
[ Horns blaring ] ♪♪ The social credit system doesn't just know if you missed a loan payment.
It knows what you bought, whom you messaged, where you went, and what you said online.
♪♪ [ Beeping ] ♪♪ Even minor infractions, like jaywalking, smoking on trains, or buying too many video games can reduce your social credit score.
So can misbehaving on social media.
♪♪ ♪♪ -Those with high scores receive honors and rewards from Sesame Credit, a financial arm of the e-commerce giant Alibaba.
♪♪ But, for the losers, there really is nowhere to go, and no way of getting there.
♪♪ Debtors on the list have been automatically prevented from flying six million times since the blacklist was launched in 2013.
♪♪ Those in contempt of court were denied sales of high-speed train tickets two million times.
♪♪ China seems to have come up with something even worse than Orwell's worst nightmare in "1984": techno totalitarianism.
[ Clank ] Big Brother, in George Orwell's "1984," keeps citizens under supervision through the telescreen.
In Huxley's "Brave New World," it's people's sex lives that are under direct state control.
Neither author imagined a world in which 24/7 surveillance would grow out of capitalism and our addiction to data-hungry smartphones.
Yet, despite coverage of all this in the West as sinister; dystopian; and, of course, Orwellian, the idea of social credit seems quite popular with the Chinese public.
♪♪ [ Sonar pinging ] ♪♪ ♪♪ -Of all the Chinese technology companies, it's this one that gives the West the most palpitations.
♪♪ This is the Shenzhen headquarters of Huawei, a vast estate of ornamental lakes and marble office buildings.
♪♪ With operations in 180 countries, Huawei is now the biggest telecommunications company in the world.
♪♪ Unusually, all of its 180,000 employees have shares in the company and they're paid an average salary of $50,000 a year... ♪♪ ...higher than the median per capita income in the United States.
♪♪ Here, at Huawei's Shenzhen headquarters, employees enjoy an hour and a half lunch break at a choice of more than 50 restaurants.
[ Sizzling ] But it's Huawei's meteoric rise as a technology exporter that has got the West's attention.
♪♪ Huawei are world leaders in artificial intelligence.
♪♪ They're also leaders, by far, in 5G, the data transfer technology that offers speeds of up to 10 gigabits a second, far faster than 4G.
♪♪ The tricky job of reassuring Western journalists that Huawei, despite US government insistence, is not a tool of the Chinese state, falls to Joe Kelly.
-So, if you accept that the future is about intelligence and that intelligence is based on data, then you move nowhere without networks across which that data can move.
That's Huawei's core business.
♪♪ -Huawei's 5G networks make possible the leap from today's Internet to the Internet of Things, in which all our devices, from our home hubs to our kitchen appliances, are connected, too.
-Looking at our airport management system, everything's connected; everything is intelligence.
There's data being collected.
♪♪ And it's not just airports, but trains.
♪♪ It's important that you know exactly where the trains are, what speed they're traveling at.
♪♪ [ Pulsing ] If you look at the map behind me, that's the control module for the city of Langan and what you're looking at is the road infrastructure, and the green lines is the flow of traffic through the city.
♪♪ If congestion happens and traffic levels build up, the artificial intelligence will be able to reconfigure travel directions to ease the flow of traffic through.
♪♪ -All very impressive, but the key point is that whoever designs the software of the future, the hardware it runs on will increasingly be made in China, by Huawei.
♪♪ -I completely understand the anxiety of the US government and some of the US policy makers and elites about Huawei.
I completely understand the anxiety.
However, they are too simplistic.
They are not knowledgeable.
They are not -- They have not got the very basic training in engineering.
-Of course they haven't.
After all, most of them are lawyers.
[ Horn blaring ] The trade war that Donald Trump declared on China in 2018 is no longer the main event.
The war that matters is the tech war.
♪♪ Until very recently, Americans confidently assumed that the future would be, to quote Apple, "Designed in California and merely assembled in China."
That is no longer plausible.
[ Buzzing ] [ Chugging ] Are the United States of America and the People's Republic of China in a new cold war, a net war?
-What we know is we know that the United States is leading and we know that this is a source of enormous investment in the United States from United States firms.
We also know that China has announced her goal of becoming dominant -- their words, not mine -- by the year 2030, so there is a competition, enormous amount of money going in, and it's important that the United States win.
♪♪ -This is a battle, a battle for global dominance, between giant American and Chinese network platforms.
♪♪ which raises the tricky question of how far the US companies, as many legislators suggest, should have their wings clipped by regulation.
♪♪ Mark Zuckerberg admits that Facebook has made its share of mistakes, but he's come up with a new and ingenious argument: If his company is too heavily regulated, or even broken up, it won't be able to compete effectively with its Chinese rivals.
♪♪ [ Siren wailing ] ♪♪ The intensity of this competition is clearly visible in Asia, Africa, and Latin America.
In some countries, the Chinese model of a state-monitored Internet has a good deal of appeal to authoritarian rulers.
[ Chittering ] For others, it just makes sound business sense to buy Chinese.
♪♪ [ Horn honking ] As founder and chairman of Econet Wireless, one of Africa's largest and most successful telecoms companies, Strive Masiyiwa is responsible for building much of the physical infrastructure on which the African Internet depends.
There is a story that went off in Reeds that China's the new empire builder in Africa and that its intentions are not entirely honorable.
-Okay, so, first of all, here are the facts, and, then, we can analyze.
When I started in this industry, all our equipment -- the network, the kit that we roll out, that we call bay stations, these towers -- 99% of that kit came from Europe and it came from the United States.
And so we kind of fast-forward today.
800 million Africans that have mobile phones today, Niall... ...90% of the kit that made that possible: China.
-And, if that had not happened, it would all have gone much more slowly 'cause it would've cost more.
-Wouldn't have happened.
♪♪ -And that's really the key point.
As the world becomes dependent on super fast 5G data transfers, it's China that's winning the network war.
♪♪ And that should worry us.
♪♪ For a networld dominated by China is very unlikely to be a world where individual freedom is a top priority.
♪♪ In this series, we've discovered how networks have the extraordinary power to unite us... -[Laughing] ♪♪ ...to spread our ideas... ♪♪ ...to take on the established interests of hierarchical power.
-[Chanting in foreign language] ♪♪ -We've also seen how they're prone to polarization and vulnerable to exploitation by malign forces.
[ Beeping ] ♪♪ Most importantly, the all-enveloping reach of modern networks means that they are the new battlefields of geopolitics.
[ Beeping ] ♪♪ The original Cold War was all about nuclear brinkmanship, shrill propaganda, and bloody proxy wars waged all over the so-called third world.
Because the Internet and the smartphone have enlarged, accelerated, and empowered social networks, the new cold war will be waged in a borderless battlefield, quite unlike the days of the Iron Curtain.
The war of the future will be waged, not on land, but in cyberspace.
Its weapons won't be nuclear missiles.
They'll be AI-enabled drone swarms capable of assassinating the key figures in a city on the basis of facial recognition.
And, in this new cold war, there is absolutely no guarantee that the democratic side will win.
♪♪ -To order "Niall Ferguson's Networld" on DVD, visit Shop PBS or call 1-800-PLAY-PBS.
This program is also available on Amazon Prime Video.
♪♪
Support for PBS provided by:











